IDaaS (Identity as a Service): what it is, how it works, and its role in modern security
7 de May de 2026When digital controls real physical processes
Industrial digital transformation has radically changed the way critical organizations operate. The arrival of Industry 4.0 has connected industrial plants, energy networks, transportation systems, hydraulic infrastructures and production environments through highly interdependent digital architectures.
Today, IoT sensors, cloud platforms, artificial intelligence, real-time analytics and advanced automation are part of the operational core of thousands of companies. This evolution has made it possible to achieve levels of efficiency, traceability and automation never seen before.
But it has also created a new structural problem: the more connected an industrial environment is, the greater its exposure to cyber risk.
The difference compared to traditional cybersecurity is critical. In OT environments and cyber-physical systems (CPS), an incident does not only compromise information. It can stop production lines, alter industrial processes, cause physical damage or directly affect national critical infrastructures.
In Industry 4.0, digital no longer only processes data. It controls the physical world. And that completely changes the rules of cybersecurity.
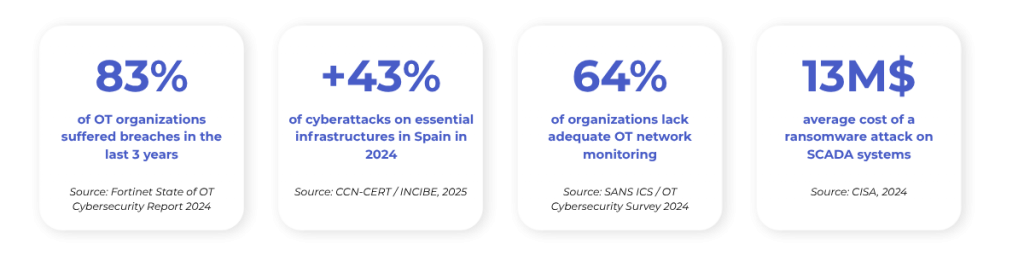
Data that define the problem
What OT, CPS environments and connected systems are in Industry 4.0
To understand the real scope of the industrial security problem, it is necessary to distinguish three concepts that are often confused.
OT environments: the infrastructure that controls industrial operations
OT (Operational Technology) environments group together the systems responsible for supervising and controlling industrial physical processes. Here we find technologies such as SCADA systems, industrial PLCs, ICS networks, industrial HMI, automation systems and smart energy infrastructures.
Unlike traditional IT systems, OT environments have radically different priorities: continuous availability, operational stability and physical integrity above any other consideration. On a corporate server, downtime implies loss of productivity. In an industrial plant, it can stop production, generate mechanical damage or compromise the physical safety of people.
CPS: cyber-physical systems that integrate software and physical operation
Cyber-physical systems (CPS) represent the natural evolution of modern industrial automation. A CPS integrates sensors, software, networks, artificial intelligence, automation and connected physical components, with the aim that digital systems interact directly with physical processes in real time.
Common examples in Industry 4.0: smart factories, industrial autonomous vehicles, smart electrical networks, automated railway systems, connected water infrastructures and advanced robotics. The problem is immediate: any digital compromise can translate into immediate physical consequences.
Connected systems: efficiency and new attack surface
For decades, many industrial infrastructures operated in a relatively isolated way. OT networks remained separate from the corporate environment and remote access was limited or nonexistent.
Industry 4.0 completely breaks this paradigm. Today industrial systems are permanently connected through IT/OT integration, remote access, cloud platforms, centralized monitoring, industrial IoT and real-time data exchange. Every new integration, sensor, external provider or remote connection introduces new risk vectors. Modern industrial automation can no longer be understood without advanced industrial cybersecurity.
Critical infrastructures in Industry 4.0: the new priority target
Critical infrastructures are those systems whose interruption could generate severe impacts on the economy, national security, public health, the continuity of essential services or social stability. In the current context, many of these infrastructures depend directly on OT environments and cyber-physical systems.
The especially exposed sectors include energy, manufacturing industry, transportation, water and sanitation, oil & gas, telecommunications, logistics and smart cities.
Evolution toward connected systems has turned these infrastructures into priority targets for industrial ransomware, sabotage, cyberespionage, advanced persistent threats (APT) and attacks against the supply chain. The concern is no longer only the theft of information. The objective is to alter real physical operations.
Real threats: incidents that changed the rules of the sector
Theory stopped being enough a long time ago. Attacks against critical infrastructures are already part of the global operational scenario.
Colonial Pipeline — USA, 2021
A ransomware attack paralyzed the largest fuel pipeline on the east coast of the United States. The entry vector was a compromised VPN password without multifactor authentication. The result was shortages in 17 states, an operational paralysis of 6 days and a ransom payment of more than 5 million dollars. (Source: CISA / U.S. Department of Energy).
The case is especially relevant because the attacker did not exploit any complex technical vulnerability: they entered with valid credentials and operated as a legitimate user.
Ukraine power grid — 2015 and 2016
Actors with state links managed to cause massive blackouts by attacking electrical distribution SCADA systems. The second attack used malware specifically designed to control industrial protocols and deactivate the electrical infrastructure, leaving 250,000 homes without supply. (Source: ENISA — European Union Agency for Cybersecurity)
Triton/TRISIS attack — Saudi Arabia, 2017
The first malware specifically designed to compromise safety instrumented systems (SIS): the physical protection mechanisms that prevent industrial accidents. Its objective was to deactivate them to force a physical incident in a petrochemical plant. Only an error in the execution of the attack prevented a catastrophe. (Source: CISA Alert AA22-083A)
Water infrastructure — USA, 2024
CISA documented throughout 2024 multiple intrusion attempts against drinking water management systems, some with confirmed access to treatment control panels. The agency issued specific alerts about the vulnerability of these systems to actors with both economic and geopolitical motivations. (Source: CISA Advisory, 2024)
Spain in the spotlight:
CCN-CERT and INCIBE documented in 2024 a 43% increase in cyberattacks on operators of essential services in Spain. The most affected sectors were energy, transportation and telecommunications. The active groups in campaigns against European infrastructures include actors linked to states with geopolitical interests in the context of the conflict in Ukraine and in the destabilization of NATO’s southern flank.
These incidents evidence a reality: most modern attacks against critical infrastructures do not begin by exploiting sophisticated technical vulnerabilities. They begin with compromised legitimate access. And there appears one of the greatest problems of current industrial security.
Structural problem: limited visibility and uncontrolled access
Many industrial organizations continue to operate with legacy architectures designed for a disconnected world. This generates structural problems that go beyond technology:
- Legacy systems without modern security capabilities.
- Limited effective segmentation between IT and OT.
- Remote access without control or audit.
- VPN with excessive privileges and no traceability.
- External providers with broad and unsupervised access.
- Lack of contextual monitoring in real time.
The problem becomes a problem of operational visibility. Many organizations cannot respond precisely to basic questions:
- Who really accesses the industrial environment?
- What systems are they using?
- What privileges do they have?
- What actions do they execute during the session?
- From what location do they access?
- Is there anomalous behavior?
In critical systems, not knowing this is equivalent to operating blindly.
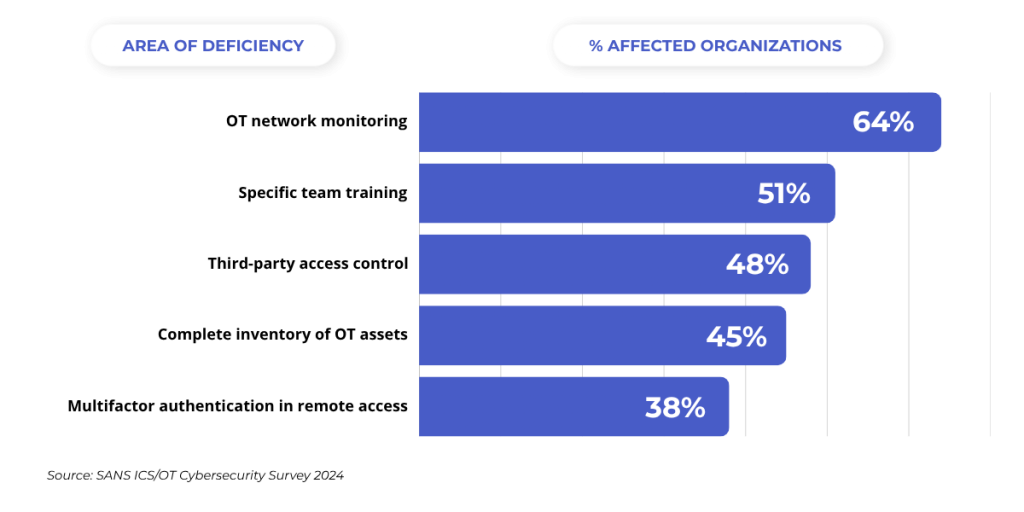
Most common security deficits in OT environments
IT vs OT: why they are not the same and why it matters
Applying IT security strategies directly to OT environments is one of the most frequent and costly mistakes. The following comparison summarizes the fundamental differences that condition any defense strategy.
| Dimension | IT Environment | OT Environment |
|---|---|---|
| Security priority | Confidentiality → Integrity → Availability | Availability → Integrity → Confidentiality |
| Lifecycle | 3–5 years | 15–30 years (active legacy) |
| Patching | Regular and automatable | Requires planned maintenance windows |
| Tolerance to interruptions | Minutes/hours acceptable | Seconds can be critical |
| Common protocols | TCP/IP, HTTP/S, TLS | Modbus, Profibus, DNP3, OPC-UA (many without native encryption) |
| Impact of an incident | Data loss / economic impact | Physical damage, risk to people |
| Standard security tools | Widely compatible | Must be adapted so as not to interrupt processes |
| Asset visibility | Generally well inventoried | Frequently incomplete or outdated |
This asymmetry explains why security in OT environments requires its own approach, with tools and processes designed specifically for the restrictions of the industrial environment.
Identity: the new industrial security perimeter
In Industry 4.0, the classic model based only on firewalls and segmentation is no longer sufficient. The new security frontier is identity.
Every access to a SCADA system, engineering station or OT infrastructure represents a possible entry point for an attacker. When a malicious actor obtains valid credentials, they bypass most traditional defenses, operate as a legitimate user and facilitate lateral movements without needing to exploit complex vulnerabilities. Colonial Pipeline demonstrated it forcefully.
That is why modern cybersecurity in OT and CPS environments must focus on controlling four dimensions in real time for each access:
- Who accesses? Robust verification with multiple factors (IAM + MFA), not only username and password.
- From where and with what context? Location, device, source network, time of access.
- With what privileges? Minimum privilege necessary at every moment (PAM with just-in-time access).
- What do they do? Continuous monitoring and complete session recording for anomaly detection (DLP + audit).
Security stops being purely perimeter-based and becomes contextual, dynamic and identity-based.
Key technologies: PAM, IAM, VDI and DLP in OT and CPS environments
To materialize identity and access control in industrial environments, four technologies form the backbone of any modern defense architecture.
PAM — Privileged Access Management
Controls, audits and protects accesses with elevated privileges: those with the greatest impact capacity on critical systems. It acts as an intermediary between the user and the system, recording every action, applying minimum privilege and managing credentials from an encrypted vault that the user never sees. 60% of attacks on industrial networks start with insecure accesses from the outside: a well-implemented PAM eliminates this vector.
IAM — Identity and Access Management
Manages who each user is, what they can do and when. It integrates identity directories, multifactor authentication, role management and governance of the access life cycle. In convergent IT/OT environments it allows unifying the management of identities of employees, providers and systems under a common framework, avoiding orphan identities with uncontrolled access.
VDI — Virtual Desktop Infrastructure applied to security
In its application to critical environments, VDI is not simply a remote desktop: it is an isolated work environment where the user operates on a virtualized session without data or credentials ever leaving the controlled infrastructure. Only keyboard, mouse, image and video events are transmitted. The critical asset is never exposed to the source device. This eliminates exfiltration by copy, download or capture, even if the user’s device is compromised.
DLP — Data Loss Prevention
Adds the control layer over what information can leave the protected environment and where it can go. It detects accidental or malicious exfiltration attempts, applies transfer policies and alerts to anomalous behavior. In OT environments it is especially relevant to control exports of process data and unauthorized communications from engineering systems.
These four technologies reach their maximum potential when they work in an integrated way within a cohesive architecture. A PAM without IAM cannot adequately verify who accesses. A VDI without DLP does not guarantee that data do not leave the environment. Integration is the differential factor.
Defense strategies: from theory to practice
Industrial Zero Trust
The Zero Trust model eliminates implicit trust. Every access must be continuously verified, regardless of whether the user is inside or outside the corporate network. NIST defines the principles of Zero Trust in publication SP 800-207, a reference for its implementation in regulated sectors.
In OT environments, the sequential control flow is:
Verify identity → Validate context → Apply minimum privilege → Monitor session → Record activity
Intelligent IT/OT segmentation
The separation between IT and OT networks remains fundamental, but it must evolve toward dynamic and monitored models. Modern segmentation must limit lateral movements, reduce exposure, isolate critical assets and control flows between environments. In many cases, the difference between a contained incident and an operational disaster depends on detection speed.
Practical case: remote access to a SCADA system
Remote access is one of the most exploited vectors in industrial environments. The comparison between models illustrates the real difference in exposure to risk.
Traditional model (direct VPN): The provider obtains broad access to the industrial network. They can move laterally between systems. There is no detailed activity log. If their credentials are compromised, the attacker inherits the same level of access. The average detection time in OT environments exceeds 200 days (Source: IBM Cost of a Data Breach Report 2024).
Model with Shielded Workspace (PAM + VDI + IAM + DLP): Access is channeled through a controlled intermediary; the destination system is never directly exposed. The provider operates only on what they need (minimum privilege). Every session is fully recorded and auditable in real time. The system credentials are in an encrypted vault: the user never sees them. Anomalous behavior is detected during the session. Lateral movement is technically made impossible.
The potential impact of an intrusion decreases drastically.
NIS2, IEC 62443 and ENS: the regulatory framework that is already enforceable
European regulation and industrial standards are hardening security requirements for critical infrastructures. Organizations no longer only have to protect systems: they must demonstrate effective control over access and the operations performed within them.
NIS2 — EU Directive 2022/2555
Expands the scope of the original regulation to more sectors and company sizes, including digital service providers, public administrations and sectors such as food, waste management and critical manufacturing. It requires:
• Access control to information systems and networks.
• Incident notification in 24 hours (alert) and 72 hours (formal notification).
• Risk management of the supply chain, including OT providers.
• Complete audit and traceability of activity.
• Mandatory multifactor authentication in accesses to critical systems.
• Direct responsibility of governing bodies.
Situation in Spain: The European Commission initiated in May 2025 an infringement procedure against Spain for failure to transpose the NIS2 Directive. Although the national law has not yet been approved, the obligations of the directive are enforceable. Organizations in essential sectors must already start their adaptation process.
IEC 62443 — The reference standard for industrial control systems
Developed by ISA and IEC, it is the global reference for cybersecurity in industrial automation and control systems (IACS). It covers policies, procedures, system design and component requirements, and defines security levels (SL-1 to SL-4) by zone and conduit. Its compliance directly facilitates that of NIS2, since both frameworks share essential requirements on access control, audit and risk management.
ENS — National Security Framework (Royal Decree 311/2022)
Establishes minimum principles and requirements for the security of information systems of Public Administrations and their providers. For organizations that supply technology or services to the Administration, compliance with ENS is a necessary condition. Inclusion in the CCN-CERT Catalogue of ICT Security Products and Services (CPSTIC) is the reference accreditation in Spain to validate solutions against these standards.
The future of Industry 4.0: more intelligence, more exposure, more complexity
Technological evolution will continue to accelerate. The coming years will bring more automation, industrial AI, digital twins, edge computing, massive IIoT, autonomous CPS and hyperconnected operations. Every advance will also increase the complexity of the attack surface.
Three trends will mark the evolution of risk:
Ransomware adapted to ICS: cybercrime groups are developing specific variants for industrial control environments, capable of identifying and blocking SCADA processes without affecting IT systems, maximizing operational impact.
AI applied to attacks: artificial intelligence accelerates the ability of attackers to identify vulnerabilities, automate reconnaissance of industrial networks and adapt malware to specific environments. What used to require weeks can today be executed in hours.
Expansion of CPS: the proliferation of collaborative industrial robotics, autonomous vehicles and connected medical infrastructure expands the attack surface in sectors where failure has direct physical consequences. CCN-CERT predicts that cyber-physical systems will be the main vector of new threat categories before 2027.
Industrial cybersecurity must evolve toward identity-based, contextual, dynamic, automated models capable of responding in real time. Because the problem is no longer only protecting networks. It is protecting digitally controlled physical operations.
Cosmikal: real control over access to critical infrastructures
In this scenario, Cosmikal materializes the principles of Zero Trust, identity control and audit in a concrete operational architecture: Endurance, the Remote Shielded Workspace (RSW).
The security model changes radically: users and providers do not access critical systems directly, SCADA, HMI, OT servers, IT assets, but through a shielded intermediary space that integrates PAM, IAM, VDI and DLP into a single solution.
This introduces multiple strategic advantages:
- The critical asset is never directly exposed. Only keyboard, mouse, audio and video events travel. Data, credentials and systems always remain within the controlled environment.
- Centralized access control. A single management point for all privileged accesses, both in IT and OT environments.
- Complete session supervision. Every action is recorded and auditable in real time, with capacity to detect anomalies during the session.
- Reduction of lateral movement. Access is limited to the necessary operational context: the provider or user works on what they need, nothing more.
- Demonstrable regulatory compliance. Endurance is included in the CCN-CERT CPSTIC, which accredits its validation against ENS and facilitates compliance with NIS2 and IEC 62443.
That architectural difference completely changes the level of risk.
Conclusion: protecting critical infrastructures requires controlling access
The defense of critical infrastructures in Industry 4.0 can no longer be approached only from the traditional IT perspective. OT environments, cyber-physical systems (CPS) and connected industrial systems require security models capable of protecting real physical operations against advanced digital threats.
In this new scenario, every identity is a possible attack vector, every remote access represents an operational risk and every session must be capable of being supervised and controlled.
Organizations that adopt strategies based on visibility, identity, segmentation and contextual control will be better prepared to protect their operational continuity.
Because in Industry 4.0, true security does not consist only of protecting systems. It consists of controlling how they are accessed, how they are used and what happens inside each session.
Sources and references
• SANS Institute: ICS/OT Cybersecurity Survey Report 2024
• CISA (USA): ICS Advisories: Colonial Pipeline / Triton / Water Sector
• ENISA: Threat Landscape for Industrial and OT Sectors 2023
• CCN-CERT: Cyber Threats and Trends Report 2024 (CCN-CERT IA-13/24)
• INCIBE-CERT: Cybersecurity Balance 2024
• NIST: Zero Trust Architecture (SP 800-207)
• IEC/ISA: IEC 62443: Industrial Automation and Control Systems Security
• European Commission: NIS2 Directive (2022/2555)
• IBM: Cost of a Data Breach Report 2024
• CCN-CERT: CPSTIC: Catalogue of ICT Security Products and Services