How Cosmikal Endurance Helps Organizations Comply with NIS2
8 de April de 2026
ITDR and PAM: how to protect identities and privileged access against advanced attacks
16 de April de 2026As organizations adopt hybrid environments, cloud applications, and remote workflows, identity management has become the backbone of corporate security. The real risk does not lie only in unauthorized access, but in the hidden complexity of identities: accumulated permissions, inactive accounts, and misassigned privileges that create silent cracks in the infrastructure. Identity Governance & Administration (IGA) emerges as the discipline that brings order to this chaos, providing full visibility, control over every access, and continuous auditing. In a landscape where attackers exploit any weakness to move laterally or escalate privileges, IGA is not a luxury, it is the essential strategy to transform identity into a secure and resilient asset. Integrated with IAM (Identity & Access Management) and PAM (Privileged Access Management), it forms a solid framework to manage risks, ensure compliance, and protect critical environments.
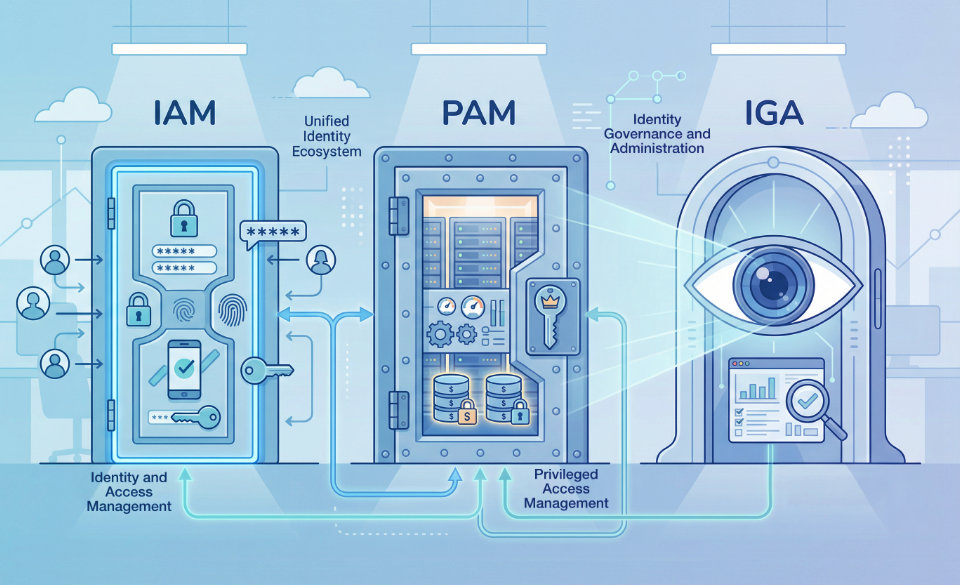
1. IAM, PAM, and IGA: understanding the identity ecosystem
In modern enterprise environments, identity security can no longer be addressed in isolation. Every access, every privilege, and every account is part of an interconnected ecosystem that requires continuous visibility and control.
While IAM enables legitimate users to efficiently access the resources they need, and PAM protects critical assets by restricting and monitoring privileged accounts, IGA acts as the brain that orchestrates the entire system. Its value lies not only in auditing and approving access, but in ensuring that every identity and permission complies with corporate policies, regulatory requirements, and security best practices.
In other words, IGA transforms identity management from an operational and reactive process into a strategic discipline that minimizes risk, maximizes traceability, and ensures operational resilience, turning every identity into a secure point within the organization’s infrastructure.
Roles in enterprise security
Although these terms are often used interchangeably, each discipline plays a distinct role within the security strategy:
| Dimension | IAM (Identity & Access Management) | PAM (Privileged Access Management) | IGA (Identity Governance & Administration) |
| Scope | Standard identity management for the entire workforce | Control and protection of privileged accounts | Comprehensive governance of all identities, roles, and access rights |
| Objective | Streamline access and improve user experience | Protect critical systems and prevent privilege abuse | Compliance, auditing, and identity risk mitigation |
| Key capabilities | Multi-factor authentication (MFA), Single Sign-On (SSO), user provisioning | Privileged session management, credential vaults, Just-in-Time access | Access certification, automated auditing, periodic reviews, compliance reporting |
| Risk mitigation | Prevents identity impersonation | Prevents lateral movement and abuse of privileged accounts | Minimizes privilege creep, removes orphan accounts, ensures full traceability |
| Regulatory contribution | Basic access logs | Control over critical systems | Compliance with NIS2, DORA, ENS, GDPR, and sector regulations |
IAM enables users to securely access the resources they need for their daily work.
PAM ensures that elevated privileges are used correctly and only by authorized individuals.
IGA acts as the brain of the system: it governs, audits, and ensures that all identity activity complies with internal policies and external regulations.
2. Key IGA functionalities and their strategic impact
Implementing IGA is not simply about optimizing technical processes, it is a leap in operational maturity that transforms how an organization manages, protects, and audits identities. A robust IGA implementation reduces risk, ensures compliance, and provides real-time visibility over all access.
A. Identity lifecycle automation (Joiner, Mover, Leaver)
The risk from orphan accounts or accumulated excessive permissions is critical, they are silent attack vectors that attackers exploit for lateral movement or privilege escalation. Lifecycle automation addresses these risks comprehensively:
• Joiner: automatic identity creation with minimum required access from day one, ensuring productivity without compromising security.
• Mover: dynamic permission adjustments when roles or departments change, eliminating unnecessary privilege accumulation (“privilege creep”).
• Leaver: immediate and complete revocation of all access across on-prem, cloud, and hybrid systems.
This automation reduces risk, accelerates operations, eliminates human error, and continuously strengthens governance.
B. Automated access reviews and certification
Traditional audits are slow and error-prone. Intelligent IGA transforms them into automated processes:
• Managers receive alerts and certification requests for relevant permissions.
• Every access is documented and formally approved.
• Continuous audit readiness is maintained for standards such as NIS2, DORA, ENS, and GDPR.
This approach simplifies audits and provides actionable insight into emerging risks and anomalies.
C. Integration into an Identity Fabric
The Identity Fabric concept connects IAM, PAM, and IGA into a unified ecosystem:
• All identities and permissions are managed centrally with consistent policies.
• Full traceability of access and privilege changes is ensured across IT and OT.
• Continuous control reduces operational risk and strengthens resilience.
This transforms identity governance into a strategic asset and enables a shift from reactive to proactive security.
3. Advanced risk mitigation with IGA
IGA goes far beyond account administration, it acts as a strategic defense mechanism that reduces critical attack vectors.
Lateral movement and insider threats
The greatest risk in any infrastructure is that an attacker can move laterally after compromising an identity. IGA provides continuous and granular control of access and privileges, ensuring that every session, role, and permission is monitored and audited in real time. This not only limits the spread of internal threats, but also minimizes the exposure of critical systems to sophisticated attacks.
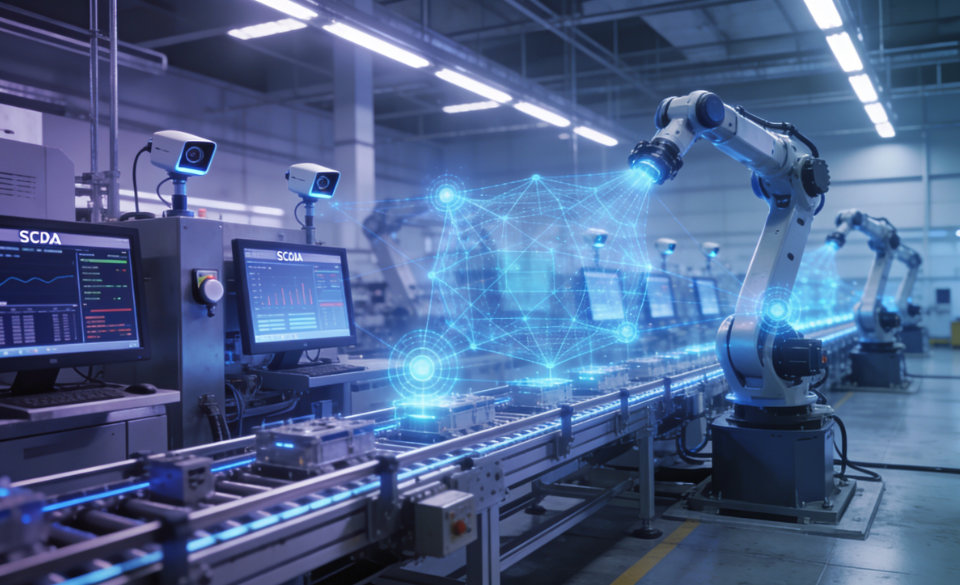
Complexity in hybrid and OT environments
Modern organizations operate in hybrid environments where traditional IT systems coexist with sensitive OT infrastructures (SCADA, ICS, industrial networks). IGA centralizes the governance of identities and permissions in these environments, ensuring that:
- Every access to industrial systems is secure, restricted, and traceable.
- International standards such as IEC 62443 are met.
- Operational risks caused by human error or misuse of privileged credentials are reduced.
This comprehensive governance ensures that security does not depend on isolated solutions, but is consistent and uniform across the entire infrastructure, reducing operational complexity and the risk of incidents.
Third-party security (Supply Chain)
Access by suppliers, contractors, and external partners represents one of the most critical risk vectors. IGA enables the implementation of Just-in-Time access strategies, strictly based on operational need and duration of access. This ensures:
- Reduction of the third-party attack surface.
- Elimination of dependency on persistent VPNs or local agents, which increase complexity and security risks.
- Full monitoring of all actions performed by third parties, with traceability and automatic auditing.
By integrating these controls, IGA transforms identity management into a proactive defense element, turning potential risks into controlled and verifiable processes.
4. IGA and regulatory compliance
Identity governance is no longer an administrative compliance exercise: today it is a strategic and operational requirement for organizations seeking resilience, traceability, and effective control of their systems. Implementing IGA allows security policies to be transformed into verifiable technical evidence, aligning daily operations with regulatory requirements.
NIS2 and ENS
These regulations require full visibility over who accesses critical systems, when, and with what permissions. IGA provides continuous auditing and detailed records, turning internal procedures into verifiable technical information. This ensures not only compliance, but also the ability to respond to security incidents and report to regulatory authorities.
DORA (Digital Operational Resilience Act)
In the financial sector, DORA imposes comprehensive digital resilience, including control over third-party identities and full traceability of access to critical systems. IGA enables automated compliance reporting, facilitating oversight of operational continuity and reducing the manual burden of audits.
GDPR and EU Data Act
Access and management of sensitive data must strictly comply with privacy rights and data export regulations. IGA ensures that every permission and every access to critical data is aligned with regulations, providing immediate evidence that the organization complies with data protection and information control requirements.
5. AI, emerging threats, and future resilience
The threat landscape is constantly evolving. The emergence of Agentic AI, AI model poisoning attacks, and malicious automation introduces unprecedented risk vectors capable of compromising identities and privileges at a speed that surpasses traditional defenses. In this context, IGA becomes a strategic tool for anticipation and mitigation, complementing IAM and PAM controls with intelligence and proactive response capabilities.
Advanced behavioral analytics
The integration of behavioral analytics enables detection of atypical patterns and deviations before they materialize into security breaches. This predictive approach transforms IGA from a reactive system into a continuous risk sensor, identifying suspicious access, potential lateral movement, and anomalies in privileged activities.
Integration with ITDR (Identity Threat Detection & Response)
Modern IGA integrates with ITDR, providing automated response to identity-related incidents. This means that any detected anomaly (ranging from unusual access to privilege escalation attempts) can be isolated, logged, and mitigated immediately, reducing exposure time and ensuring operational continuity.
Protection of critical IT and OT infrastructures
Organizations managing critical systems, both IT and OT, require comprehensive protection against sophisticated threats. IGA, integrated into a coherent security ecosystem, ensures that access to sensitive systems remains strictly controlled and traceable, even in the face of attacks driven by generative AI. This guarantees uninterrupted critical operations and keeps infrastructure inaccessible to malicious actors.
Anticipating the future of identity
In the coming years, the evolution of generative and autonomous AI will require IGA not only to manage identities, but to orchestrate digital resilience proactively, ensuring that every access and every privilege is continuously verified, audited, and adapted to an ever-changing threat landscape.
6. Best practices and strategic recommendations
•Implementing IGA effectively requires more than technology: it demands an integrated approach combining processes, controls, and a strong security culture. The following recommendations reflect best practices for organizations seeking resilience, efficiency, and continuous compliance:
- Adopt a Zero Trust identity-based model: every access must be validated, authenticated, and logged, reducing the attack surface and ensuring no privilege is granted by default.
- Centralize identity and privilege management: consolidating administration into a single control point reduces operational complexity, avoids duplication, and enhances traceability of every access.
- Automate the full lifecycle of accounts: onboarding, role changes, and permission revocation are managed automatically, minimizing human error and eliminating privilege accumulation (“privilege creep”).
- Integrate auditing and periodic access certification: regular and automated reviews ensure compliance, continuous control, and verifiable audit evidence.
- Combine IGA, IAM, and PAM into a cohesive ecosystem (Identity Fabric): this integration enables consistent policy enforcement across IT and OT, improving efficiency, reducing risks, and strengthening operational resilience.
- Incorporate behavioral analytics and anomaly detection: anticipating emerging threats through advanced monitoring and proactive alerts transforms IGA into a predictive system capable of responding to risks before they impact the organization.
By applying these practices, IGA evolves from a simple administrative process into a strategic security engine capable of protecting identities, optimizing operations, and ensuring continuous regulatory compliance.
Conclusion
IGA goes beyond simple account administration: it is a strategic pillar of modern security. When integrated with IAM and PAM, it forms an intelligent and auditable identity ecosystem capable of reducing the attack surface, ensuring regulatory compliance, and strengthening operational resilience against current and emerging threats.
Implementing IGA is not just a technical project, but an investment in control, visibility, and continuous protection: from individual identities to the most critical systems, every access and privilege is subject to intelligent supervision. In an environment where attacks are increasingly sophisticated and infrastructure more interconnected, IGA becomes the backbone of digital defense, transforming identity into a strategic asset that drives security, efficiency, and business continuity.
Cosmikal and the realization of a resilient identity strategy
After analyzing in depth the functions, impact, and evolution of identity governance (IGA), its integration with IAM and PAM, and its role in risk mitigation and regulatory compliance, it is important to highlight that theory only gains value when translated into effective, operational controls in production environments. That is precisely what a modern security architecture proposes: identities, access, and privileges managed in a secure, traceable, and auditable way, from the user to the most critical systems.
In this context, Cosmikal’s solutions are not conceived as isolated tools, but as integrated components of a corporate security architecture, where identity and privilege control, privileged access protection, and continuous governance are fundamental elements.
- Endurance, the shielded remote workspace, incorporates IAM, PAM, VDI, DLP, and access controls as part of a defense-in-depth strategy. It operates as a secure and isolated control point that prevents lateral movement and exposure of critical systems, while providing strong authentication, full traceability, and real-time technical compliance.
- Ranger, the shielded local workspace, extends these principles to physical workstations through thin clients and non-persistent environments, ensuring that even direct access to sensitive systems is governed, controlled, and securely restored in every session.
Alignment of IGA, IAM, and PAM practices
These approaches reflect a holistic and practical vision of identity and governance, where IGA is not just a compliance concept, but an operational layer of real protection integrated with access control, auditing, session isolation, and continuous monitoring, transforming identity security into business resilience.
By aligning IGA, IAM, and PAM practices with architectural solutions like those offered by Cosmikal, organizations can move from a reactive defensive posture (focused on alerts and patches) to a proactive, auditable, and adaptable security strategy, capable of meeting regulatory requirements such as NIS2, ENS, or DORA, as well as emerging threats driven by automation and artificial intelligence.
Ultimately, identity governance ceases to be a theoretical requirement and becomes a key element of corporate security architecture, one that delivers control, visibility, and continuous protection, from user identity to the organization’s most valuable assets.