Traditional PAM fails in OT environments
26 de March de 2026
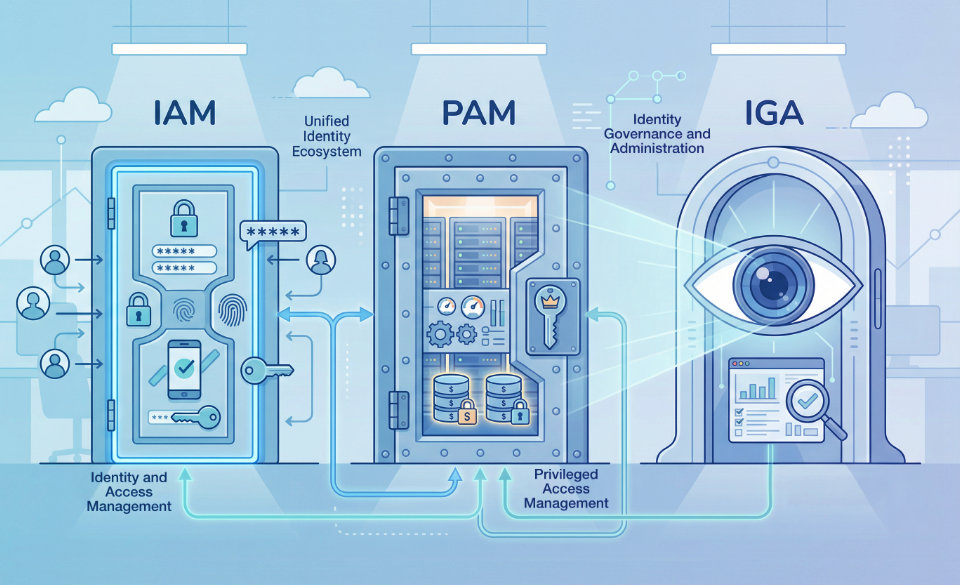
IGA (Identity Governance and Administration): the brain of security in modern environments
9 de April de 2026The primary objective of Directive (EU) 2022/2555 (known as NIS2) is to standardize the level of cybersecurity across all European Union countries. Additionally, this directive sets a countdown for mandatory compliance for all affected entities, which are those classified as essential or important.
Essential Sectors under NIS2
- Energy
- Transport
- Banking
- Financial market
- Infrastructure
- Healthcare
- Supply and distribution
- Digital infrastructure
- Online marketplaces
- Online search engines
- Cloud computing services
Additional essential
- Beverages and wastewater
- Product/Prepared goods manufacturers
- Space infrastructure and services
Important
- Food production, processing, and distribution
- Manufacturing of medical chemicals, computers, electronics, optical products, electrical equipment, machinery and equipment, motor vehicles, and transport vehicles
- Heating, electricity market, and oil storage
- Waste management
Why is Cosmikal Endurance the Solution I Need?
Cosmikal Endurance is a Privileged Access Management (PAM) solution that enables the Information Security Manager to maintain full control over access to the organization’s critical assets.
By integrating this technological solution into the organization’s infrastructure, compliance with NIS2 is ensured across multiple areas:
Article 21: Cybersecurity Risk Management Measures
Entities are required to implement appropriate and proportionate technical and organizational measures to manage risks to the security of network and information systems.
Cosmikal Endurance ensures that access to these systems is securely managed and monitored, reducing the risk of unauthorized access.
Article 23: Reporting Obligations
Promptly reporting significant incidents affecting the service is another of the established obligations.
This privileged access manager detects, responds to, and recovers from cybersecurity incidents by controlling and monitoring access, which is critical for incident mitigation.
Paragraph 49: Strengthening Cyber Resilience with Comprehensive Cyber Hygiene Policies
This solution manages and secures privileged access to the network and information systems, promoting cyber hygiene policies.
This ensures that only authorized users have access to critical systems, enforces periodic updates of privileged account credentials, and conducts detailed audits of privileged activities.
Párrafo 51: Aprovechamiento de tecnologías innovadoras para mejorar la ciberseguridad
Endurance integrates innovative technologies, including Artificial Intelligence, to streamline the detection and prevention of cyberattacks.
This enables the automation of credential management and monitoring of user activities, ensuring compliance with data protection regulations.
Paragraph 57: Promoting Active Cyber Protection in National Strategies
It prevents unauthorized access by managing and monitoring all access, detecting threats in real time, and mitigating them.
Párrafo 83: Garantizar la seguridad de los sistemas de red y de información
Endurance can help strengthen the security of networks and information systems for both essential and important entities, whether managed internally or outsourced. It achieves this by controlling and auditing access to these systems.
Paragraph 89: Cyber Hygiene and Integration of Security Technologies
Endurance promotes cyber hygiene practices through access management based on zero-trust principles. By facilitating necessary updates and ensuring secure configurations, network segmentation is achieved.
Additionally, it is possible to integrate advanced cybersecurity technologies such as Artificial Intelligence or machine learning, which naturally enhance its defensive capabilities.
Paragraph 98: Encryption as a Standard for Communication Security
This technological solution supports the principles of privacy by design and ensures that only authorized personnel can access communication systems and sensitive data. In this way, it complies with the directive’s emphasis on encryption without compromising end-to-end encryption methods.
Paragraph 102: Structured Approach to Incident Reporting and Management
Endurance enables rapid detection and reporting of significant incidents by tracking and analyzing privileged user activities. It also notifies and provides detailed audit logs, which are key for early warnings, incident reporting, and final reports.
Do you want to comply with NIS2 using a reliable, robust system that allows you to keep all your organization’s assets under control? Discover Endurance.