The revolution of Cyber-Physical Systems (CPS): the awakening of physical intelligence
5 de March de 2026
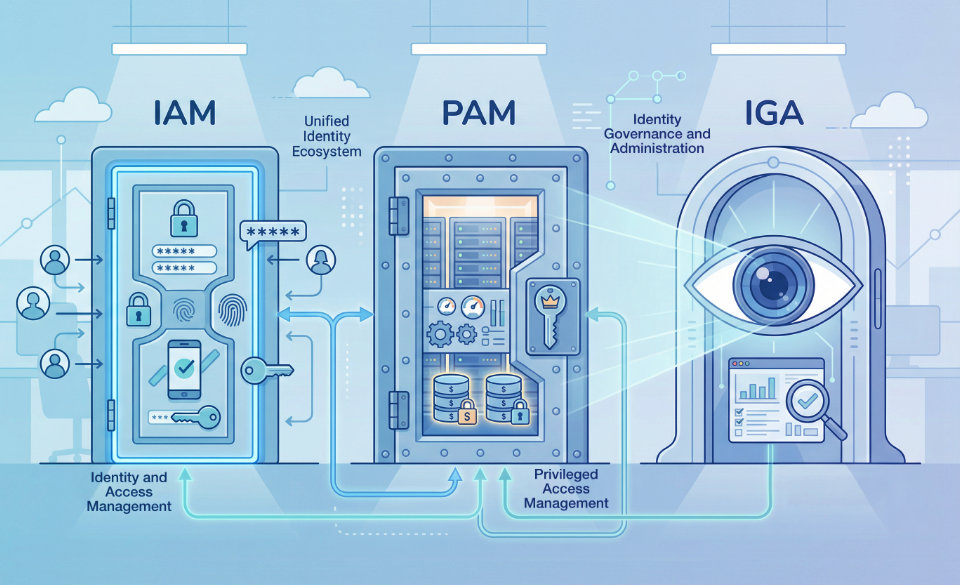
Three critical pillars of enterprise security
19 de March de 2026Since January 17, 2025, Regulation (EU) 2022/2554 — Digital Operational Resilience Act (DORA) has been fully applicable and enforceable across the European Union. It is not a voluntary framework: it is hard legislation that redefines how financial institutions and their technology providers manage ICT risk, cyber incidents, and business continuity.
In this new context, digital resilience ceases to be merely an “audit topic” and becomes a market requirement, monitored by European supervisors and accompanied by significant sanctions in the event of non-compliance. For organizations capable of supporting banks, insurers, fintechs, or cloud providers on this journey, DORA opens a clear window to deliver value and position themselves as leaders in operational resilience.
1. What is DORA?
Technically, DORA is a European regulation on digital operational resilience that establishes mandatory requirements across five major domains: ICT risk management, incident management and reporting, resilience testing, third-party risk management, and mechanisms for sharing threat intelligence.
Its objective is to ensure that technological failures, cyberattacks, or disruptions affecting suppliers cannot paralyze the financial system or jeopardize market stability.
- January 16, 2023: DORA enters into force (start of the “countdown”).
- January 17, 2024: first wave of technical standards and delegated acts.
- July 17, 2024: second wave of standards and supervisory delegated act.
- January 17, 2025: DORA becomes fully applicable to entities and providers.
In parallel, the European Commission and the European Supervisory Authorities (ESAs: EBA, ESMA and EIOPA) have been publishing Regulatory Technical Standards (RTS) and Implementing Technical Standards (ITS). This operationalizes the regulation through metrics, reporting formats, incident classification criteria, and the methodology for designating critical providers.
2. Who does DORA apply to?
DORA is a regulation, not a directive, which means it is directly applicable across all EU Member States without requiring national transposition. Its scope is broad and covers both financial entities and certain ICT providers delivering essential services to the sector.
Financial entities covered
Among others, DORA applies to:
• Credit institutions and banks.
• Payment service providers and electronic money institutions.
• Investment firms, asset managers, fund management companies, and custodians.
• Insurance and reinsurance companies.
• Market infrastructures (CCPs, CSDs, trading venues, data repositories).
• Pension institutions (IORPs), UCITS entities, AIFMs, and crowdfunding service providers.
• Crypto-asset service providers and issuers of asset-referenced tokens (in coordination with MiCA).
There are no full exemptions based on size: micro-enterprises are also included within the perimeter, although some obligations may be proportionally adapted.
ICT Providers: the Critical Third-Party Providers (CTPPs)
DORA introduces a specific supervisory regime for “Critical ICT Third-Party Providers” (CTPPs): providers whose ICT services are so relevant that a failure could have systemic impact.
In November 2025, the ESAs published the first list of 19 CTPPs, including major cloud providers, data center operators, telecommunications companies, and specialized technology providers for financial services.
This means:
• If you are a financial institution in Europe, DORA applies to you.
• If you are a key technology provider (cloud, data analytics, cybersecurity, connectivity, core banking SaaS, etc.) and appear on the CTPP list, you fall under direct European supervision, with obligations related to transparency, testing, and cooperation with supervisors.
3. What does DORA technically require? The five pillars
DORA structures its requirements around a comprehensive resilience architecture, with controls ranging from governance to advanced testing and third-party oversight. It is not simply a condensed ISO 27001, but rather a regulatory overlay that reinforces, structures, and makes the entire digital resilience stack auditable.
a) ICT risk management
Entities must implement a formal ICT risk management framework covering the entire lifecycle of digital services. Requirements include:
- Clear governance structures with defined roles and responsibilities at board and executive level.
- Documented ICT risk policies aligned with business strategy.
- Inventory and classification of assets, processes, and critical services.
- Continuous identification, analysis, assessment, treatment, and monitoring of ICT risks.
- Explicit risk appetite and metrics, with thresholds and escalation mechanisms.
b) Incident management and reporting
DORA strengthens obligations to detect, manage, and report ICT-related incidents according to harmonized European criteria and timelines.
This includes:
- Classification of incidents according to impact, criticality, and affected services.
- Notification of major incidents to competent authorities using RTS/ITS templates and timelines.
- Coordination with CSIRTs and other relevant authorities.
- Detailed records, telemetry, and traceability enabling forensic analysis and supervisory oversight.
Although aligned with frameworks like NIS2, DORA introduces its own reporting model tailored to the financial sector and subject to periodic reviews.
c) Digital resilience testing
It is not enough to “have controls”; organizations must prove they work under pressure.
DORA requires periodic operational resilience testing, including:
- Structured testing plans covering critical services, processes, and dependencies.
- Business continuity and disaster recovery exercises based on realistic scenarios.
- Threat-led penetration testing (TLPT) under supervisory oversight for designated entities.
- Documented remediation plans and retesting procedures.
d) ICT third-party risk management
This is one of DORA’s most transformative elements: ICT vendor management becomes central to resilience.
Entities must:
- Maintain a complete inventory of ICT providers and outsourced services.
- Classify services according to their importance and risk to business continuity.
- Include contractual clauses covering supervision, reporting, testing, and termination rights (“exit strategies”).
- Periodically assess vendor performance using KPIs, SLAs, and control evidence.
Meanwhile, CTPPs fall under direct ESA supervision, which can request information, perform inspections, and require corrective measures.
e) Threat intelligence information sharing
DORA actively promotes Threat Intelligence Sharing agreements among financial entities, providers, and authorities within trusted frameworks.
Objectives include:
- Anticipating coordinated attack campaigns targeting multiple institutions.
- Sharing TTPs (tactics, techniques, procedures) and relevant IOCs.
- Improving sector-wide prevention and response capabilities while reducing duplication of analytical effort.
4. How is DORA applied in practice?
DORA operates as a continuous program of supervision, evidence generation, and improvement. The European Supervisory Authorities (EBA, ESMA, EIOPA) act as Lead Overseers of CTPPs and coordinate with national supervisors to review implementation across financial entities.
Supervisory powers
Authorities have extensive powers including:
- Information requests and documentation submissions.
- Off-site assessments and model reviews.
- On-site inspections, directed tests, and executive interviews.
- Formal recommendations, corrective measures, and potentially significant financial penalties.
During 2025–2026, the focus has shifted from publishing guidance toward conducting inspections and resilience tests, with a maturity horizon extending beyond 2027.
Technical frameworks and standards
Delegated acts and technical standards define:
- Incident classification and reporting methods.
- Minimum contents of ICT risk frameworks and testing plans.
- Criteria for identifying and supervising CTPPs.
- Reporting formats for risks, tests, and incidents.
For organizations, this translates into implementing policies, procedures, governance tools (GRC, IRM), and dashboards capable of demonstrating compliance during audits and supervisory reviews.
5. Real benefits for the financial sector (and end users)
Beyond regulatory pressure, DORA is driving tangible improvements in the robustness of the European financial system.
System robustness and systemic risk reduction
- Better visibility into ICT supply chains and critical dependencies.
- RTO and RPO targets aligned with real operational requirements and tested in practice.
- Faster incident reporting and recovery processes with coordinated information sharing.
Sector collaboration and technological maturity
- Threat intelligence sharing enabling anticipation of coordinated attacks.
- More consistent resilience testing and crisis simulations.
- Adoption of modern architectures focused on resilience, observability, automation, and secure-by-design principles.
Organizations that adopt DORA proactively often achieve more stable and trustworthy technology environments.
6. Evidence that DORA is already operational
The clearest evidence that DORA is not theoretical is that authorities have already designated and published the first list of critical ICT providers and started supervisory activities.
In parallel:
- Financial entities must report major ICT incidents using standardized templates and deadlines.
- Formal reviews of ICT risk frameworks, resilience testing, and third-party risk management are underway.
- Non-compliance can result in substantial fines, not just warnings.
Resilience maturity tables, continuity indicators, and RTO/RPO metrics are already being assessed under DORA criteria by supervisors and auditors.
7. Recent regulatory milestones (2025–2026)
DORA continues evolving through an active regulatory agenda.
Key milestones include:
• June 2025: delegated acts refining ICT risk metrics and supervisory team structures.
• November 18, 2025: ESAs publish the first list of 19 CTPPs, activating direct European oversight.
• 2026: progressive integration of DORA into the Supervisory Review and Evaluation Process (SREP) and consolidation of continuous monitoring methodologies.
For organizations, 2025–2026 are not transitional years: they represent full implementation with clear expectations for measurable results and evidence.
8. DORA is not “just another regulation”
DORA represents a structural shift in how digital resilience is measured and governed.
Key implications:
- Compliance templates alone are insufficient; supervisors expect metrics, operational evidence, and real testing results.
- Resilience must be demonstrated through measurable indicators such as RTO, RPO, availability, detection time, and response time.
- The ICT supplier chain must be visible, quantified, and auditable, from contracts to operational performance.
For 2025, a CISO whose cybersecurity program is not aligned with DORA is not only out of regulatory time but also losing competitiveness against organizations that turn resilience into a trust signal for clients, investors, and the market.
9. Cosmikal as a strategic partner in the DORA context
In an environment where DORA requires operational evidence, resilience metrics, access governance, and control of critical providers, Cosmikal offers concrete capabilities that can help organizations translate regulatory requirements into operational practice through proven and certified solutions.
Solutions oriented to operational resilience and access control
Cosmikal designs cybersecurity products focused on protecting access, securing IT and OT assets, and shielding work environments from advanced threats, aligning with multiple DORA pillars such as risk management, monitoring, traceability, and third-party control.
- Endurance integrates a Shielded Remote Workspace, combining PAM, VDI, DLP, IAM, and session controls with protocol isolation, providing full traceability and control over access to critical systems.
- Ranger provides a Shielded Local Workspace through thin clients, ensuring access to assets always occurs from controlled and restorable environments, reducing endpoint-originated attack vectors.
These capabilities align with DORA requirements such as access governance, segregation of duties, privileged activity monitoring, and reduction of attack surface, all of which are measurable and auditable in regulatory inspections.
Certifications and official recognition
A milestone reinforcing Cosmikal’s relevance in this context is the CPSTIC 2025 Award granted by the Spanish National Cryptologic Center (CCN-CERT) in the SME category. Additionally, Endurance has been included with LINCE certification within the PAM taxonomy of the CPSTIC catalogue (and soon also within the VDI category).
These recognitions validate the technical robustness, interoperability, and security of the solutions, providing independent evidence aligned with best practices promoted by operational resilience frameworks such as DORA.
Contribution to broader regulatory compliance
Although DORA does not prescribe specific products, many of its obligations, such as incident management, access governance, activity logging, ICT supplier oversight, and resilience testing, require technologies capable of:
- Capturing and storing session and access logs with integrity and traceability.
- Controlling and restricting privileged access to critical systems.
- Isolating access environments to prevent attack vectors from compromised devices.
- Generating technical evidence usable in audits, incident reports, and regulatory reviews.
Cosmikal solutions are specifically designed to provide auditable access control and monitoring capabilities, enabling organizations to translate DORA regulatory requirements into tangible operational evidence.
Strategic positioning and market validation
Technical recognition, including the presence of Cosmikal solutions in the CCN cybersecurity product catalogue, and participation in industry events such as ENISE 2025 demonstrate Cosmikal’s position as a consolidated cybersecurity provider in Spain, delivering solutions demanded by critical sectors that must comply with digital resilience regulations.